Microsoft is a primary target for threat actors, who scour Microsoft applications for weaknesses. Our security research team at Adaptive Shield recently discovered a new attack vector caused by a vulnerability within Microsoft’s OAuth application registration that allows attackers to leverage Exchange’s legacy API to create hidden forwarding rules in Microsoft 365 mailboxes.
To understand this new attack vector, you must understand the key components therein. These include hidden forwarding rules and SaaS-to-SaaS app access, all of which amount to a malicious SaaS rootkit that can infiltrate users’ accounts and control their mailboxes — without the users’ knowledge.
Learn more about the top use cases to secure your entire SaaS stack.
Hidden Forwarding Rules
Inbox rules are actions that occur based on preset conditions within a Microsoft mailbox. Users or admins can use forwarding rules to trigger protocols based on different attributes of the user’s inbox.
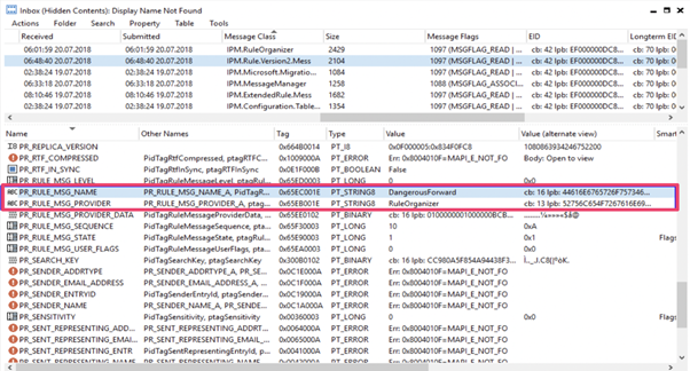
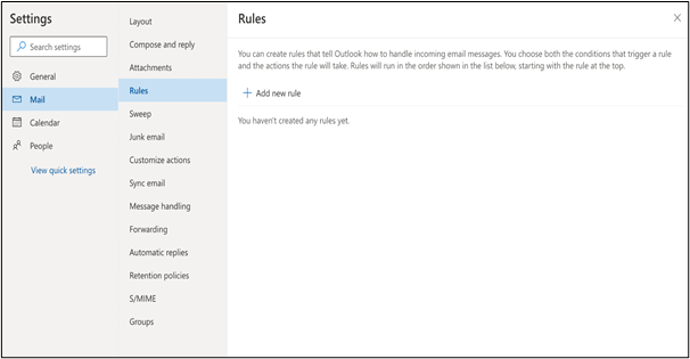
Hidden forwarding rules (Figure 1) were first discovered by Compass Security’s Damian Pflammater in 2018. He covered the discovery and Microsoft’s response in a blog post titled “Hidden Inbox Rules in Microsoft Exchange.” These rules are fully functional and can be seen on the back end. However, they are not visible common interfaces such as email clients, an admin dashboard, or an API (Figure 2).
SaaS-to-SaaS Access Through OAuth 2.0
SaaS-to-SaaS app access, also referred to as third-party app access, describes the conditions under which one app can connect to another app and, in doing so, gain access and permission to different information and settings. The OAuth 2.0 mechanism simplifies the process of authentication and authorization between consumers and service providers through a seamless process that allows users to quickly verify their identities and grant permissions to the app. The app is then allowed to execute code and perform logic within its environment behind the scenes.
In many instances, these apps are completely harmless and often serve as a valuable business tool. In other instances, these apps can act as malware, similar to an executable file.

The Next Evolution: An Attack Method Through SaaS
With this SaaS rootkit, threat actors can create malware that lives as a SaaS app and can infiltrate and maintain access to a user’s account while going unnoticed.
While bad actors can’t find Exchange Legacy scopes that can used to add programmatically online hidden forwarding in the Microsoft UI, they can add them through a terminal script.
The attacker’s job is simple: Create an app that looks credible, add the legacy scope protocols removed from the UI to the app (exploiting the vulnerability that the Adaptive Shield team uncovered), and send an offer to users to connect to it. The user will see an OAuth app dialogue box on the official Microsoft site, and many will likely accept it (Figure 4).
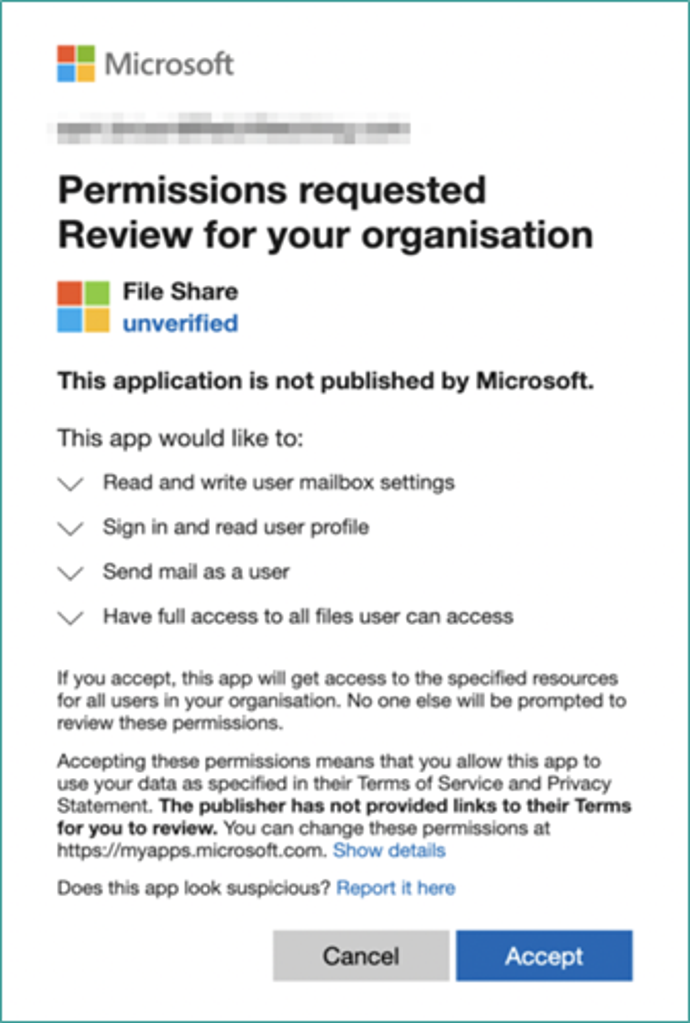
Once a user accepts, the bad actor receives a token that grants permission to create forwarding rules and hides them from the user interface like a rootkit.
An attack through these hidden forwarding rules should not be mistaken for a one-off attack but, rather, the start of a new attack method through SaaS apps.
Microsoft Response
In 2022, Adaptive Shield contacted Microsoft about the issue, Microsoft in response said that the issue has been flagged for future review by the product team as an opportunity to improve the security of the affected product.
How to Best Mitigate a SaaS Rootkit Attack
There’s no bulletproof way to eliminate SaaS rootkit attacks but there are a few best practices that can help keep organizations more protected.
- Monitor third-party app access and their permissions to ensure that apps are legitimate and given only the access they require.
- Track activities and be on the lookout for new inbox rules to identify any new connections from untrusted domains.
- Disable third-party app registrations where possible to reduce risk.
Conclusion
Hidden forwarding rules are still a threat, even more so when they appear through the trusted Microsoft website. The traditional controls that were created to stop malware have struggled to keep up with the evolution of malware and the new attack vector that can exploit any SaaS app, from M365 to Salesforce to G-Workspace, etc. Organizations should utilize native security configurations to control the OAuth application installations across SaaS apps to protect users from malicious attacks like these.
Get Forrester’s SSPM Report, “Embrace aParadigm Shift In SaaS Protection: SaaS Security Posture Management.”
About the Author

A former cybersecurity intelligence officer in the IDF, Maor Bin has over 16 years in cybersecurity leadership. In his career, he led SaaS Threat Detection Research at Proofpoint and won the operational excellence award during his IDI service. Maor got his B.Sc. in computer science and is CEO and co-founder of Adaptive Shield.
- SEO Powered Content & PR Distribution. Get Amplified Today.
- Platoblockchain. Web3 Metaverse Intelligence. Knowledge Amplified. Access Here.
- Source: https://www.darkreading.com/vulnerabilities-threats/saas-rootkit-exploits-hidden-rules-in-microsoft-365-



