Ledger’s objective has always been to deliver uncompromising security and usability to anyone exploring the world of digital assets. Of all the self-custody solutions to keep your private keys safe and accessible, our hardware devices are second to none.
When using a Ledger device, you are guaranteed that no one can interact with your private keys without your consent. Ever. Any interaction with the secrets held by your device will always require a manual action on your end: it’s the core principle behind your hardware wallet’s security.
But pure technical security is only part of the equation, and the user experience in crypto has much room for improvement. The first question every newcomer asks when going down the self-custody path and generating their Secret Recovery Phrase is: “What the heck do I do with these 24 words?”.
While some people may memorize their Secret Recovery Phrase, I don’t have this kind of trusting relationship with my brain. The standard advice so far has been to write them down on a piece of paper or in a metal store, and to keep it in a secure location. These options are not ideal, and make it harder to increase crypto-adoption.
In order to make self-custody more easily accessible, Ledger has brought forward a new answer: Ledger Recover.

In short, Ledger Recover is a self-custody solution to securely back up your Secret Recovery Phrase to the cloud, allowing you – and only you – to restore it to your hardware device in the future.
Reading this, your crypto-spidey senses should be tingling: Cloud and Secret Recovery Phrase backup don’t usually go well together. But the reality is that a cloud backup can be a perfect solution, as long as it is well-designed and entirely secure.
There are several reasons why other cloud backups solutions have a bad reputation: the Secret Recovery Phrase is at some point unencrypted (whether on your computer, browser, or server), the backup is usually held by a single entity, and it’s too easy to access it.
While designing Ledger Recover, we carefully considered these objections (and more) and succeeded in building the most secure solution for crypto users looking for a simpler yet robust personal OpSec.
To understand its rather complex design, let’s rebuild it together from scratch over the course of a few blog posts. Our starting point will be this simple idea:
I have a Secret Recovery Phrase on a bulletproof hardware wallet and would like to back it up online, without compromising security or control.
First, let’s look at how you could do this yourself, moving away from having your Secret Recovery Phrase written on a piece of paper. Then, we’ll dig a little deeper into how Ledger Recover does the same, or even better, online.
In this blog post and various Ledger publications, we often mention the ‘Secret Recovery Phrase’, the ‘seed’ and the ‘entropy’, somewhat interchangeably.
While not being strictly equivalent, these three concepts are tightly linked, and their usage depends on the technical context.
Want to learn more about this? Ledger Academy has got you covered!
Splitting the Secret Recovery Phrase: A key way to keep control
The first thing you want to avoid is giving your entire Secret Recovery Phrase to any single entity, as secure or trustful as they might be. Once again, self-custody is critical for effective fund management, so giving your entire Secret Recovery Phrase to anyone is never acceptable.
Any weakness in the system, whether human or machine, would compromise all your funds, or make you lose your backed-up Secret Recovery Phrase. This is why cloud backups have such a bad reputation in Web3, and why any standard cloud backup system is unsuitable for handling Secret Recovery Phrases.
The classic way to avoid this loss of control is to distribute the risk by splitting your Secret Recovery Phrase into multiple parts, also called shares or fragments. Each share is only a part of your secret, so they will need to be combined to obtain the original Secret Recovery Phrase. Individually, they are useless. Therefore, these shares can be given separately to different people such that no single entity can recombine the Secret Recovery Phrase.
If you need to recover your Secret Recovery Phrase – maybe because you’ve lost your hardware device and need to initialize a new one – you would ask each ‘backup friend’ for their share.
Now, what’s the best way to split your Secret Recovery Phrase?
One option is to write your 24-words on a piece of paper, then cut it into three parts, for example, which are each given to different people to hold safely. In this setup, all three of your friends would have to collude to steal your hard-earned crypto.

This kind of naive split is easy to perform, but is far from ideal. While it does not readily submit control of your funds, each share reveals a big part of your Secret Recovery Phrase, which heavily reduces the difficulty of guessing the rest of it. The situation is even worse if any two of your backup friends collude because they have enough information to perform a brute-force attack to find the remaining part. Finally, if even a single one of your friends has genuinely lost their share, then the only way for you to recover it is to’ brute-force it’ yourself.
There is also a question of how the split is done: You don’t want anyone eavesdropping while you process your most valuable secret. It must be done in a secure and safe environment.
How Ledger Recover does it: Shamir Secret Sharing
Luckily, in the case of digital secrets, cryptography has a better way of splitting than the method above in the form of the Shamir Secret Sharing scheme (abbreviated SSS later).
Using SSS to split your Secret Recovery Phrase guarantees that each share provides no extra information on the rest of the Secret Recovery Phrase. In other words, the difficulty of guessing the entire Secret Recovery Phrase remains the same whether you have prior knowledge of one of the shares or not.
On top of that, SSS easily supports m-of-n setups, which means you can generate n shares to be distributed but only need m shares to rebuild your Secret Recovery Phrase. In other words you can afford to lose some parts of your backup without impacting its restoring capabilities. This added redundancy is very important to create a resilient system.
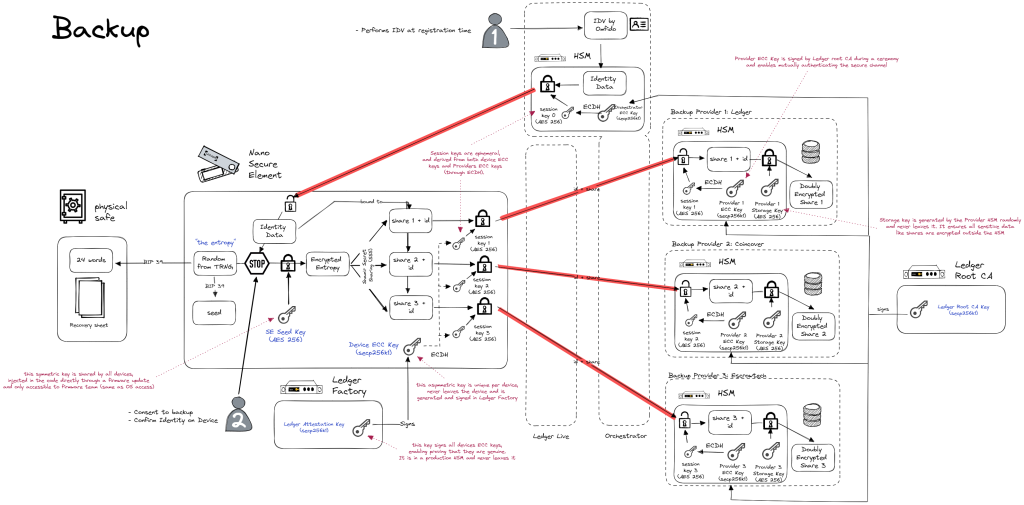
In Ledger Recover, we have chosen to use a 2-of-3 scheme. It means at least two shares are required to rebuild the original Secret Recovery Phrase. In this way, no single backup provider has control of your secret, but the backup is resilient to the loss of one provider.
The initial three backup providers are:
– Coincover, a company based in the UK,
– EscrowTec, a company based in the US,
– And us, Ledger, based in France.
In the future, we also intend to have more backup providers to choose from. This will allow users to build the best setup for themselves.
You can find an excellent introduction to SSS here, but let us give you a feel of how it works for a simple 2-of-n scheme.
Using our elementary school math courses, we know that only one straight line goes through two distinct points, but an infinite number of straight lines go through a single point.
We’ll be using this to generate the shares of your secret:
- Let’s say the secret is the value
s - We then pick a random straight line that goes through the point
(0,s) - We can define the
nshares as the points of the random line at indices{x=1, x=2, x=3, …, x=n}
Now, if you have any two shares, you can easily reconstruct the only straight line that goes through them. You will have retrieved your initial secret by intersecting this line with the y-axis (x=0).
But if you only have a single share, an infinite number of straight lines go through it, so the secret could be any number, and guessing the right line is as difficult as guessing the secret in the first place!
In this blog post and various Ledger publications, we often mention the ‘Secret Recovery Phrase’, the ‘seed’ and the ‘entropy’, somewhat interchangeably.
While not being strictly equivalent, these three concepts are tightly linked, and their usage depends on the technical context.
Want to learn more about this? Ledger Academy has got you covered!
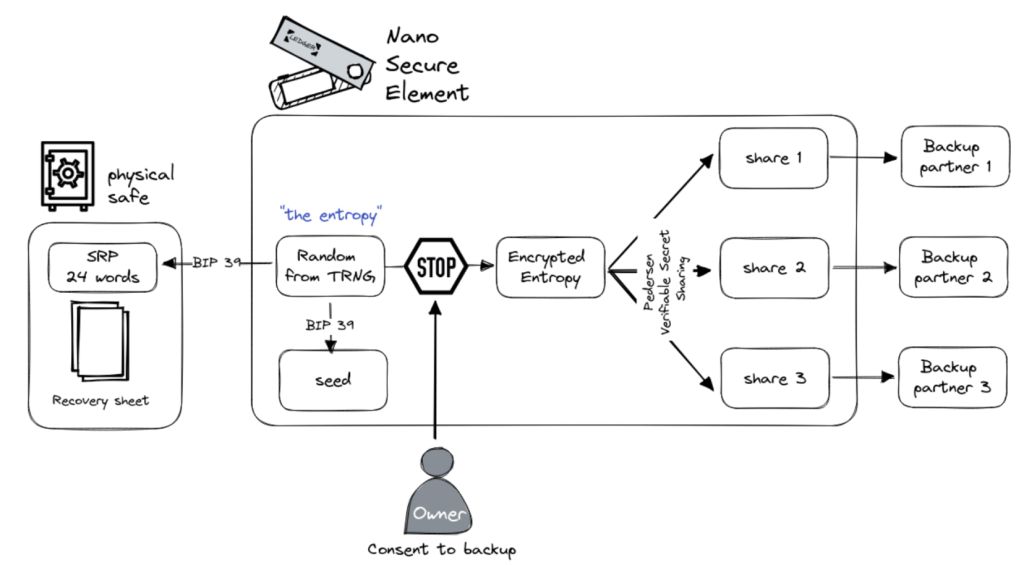
As mentioned before, this cryptographic process needs to be done in a protected environment so no part of the secret is ever revealed to potential attackers. When using Ledger hardware wallets, the share computation is entirely done inside the Secure Element, under the strict control of the user pin code. This ensures that no external software or machine can ever access the Secret Recovery Phrase during the backup process. More on this in the next blog posts of the series!
Ok, let’s back up a bit
We’ve learned that when designing a backup, it is good practice to split your secret into multiple shares and distribute them to different backup providers (friends, trusted entities, etc.). This is compatible with self-custody, as you remain the only person able to retrieve the entire seed phrase without depending on third-party approval to use your funds. However, the split scheme cannot be left to chance, as it can drastically reduce your overall security if chosen incorrectly.
Thanks to a 2-of-3 setup using Pedersen Verifiable Secret Sharing scheme, we have made Ledger Recover more resilient to backup provider failures. By performing the share split entirely inside your hardware wallet’s Secure Element, the user’s Secret Recovery Phrase is not vulnerable to malicious parties. In addition, we can safely verify that backups are correctly generated, which is crucial if we want to restore them in the future!
Now it’s time for Part 2 to address the next elephant in the room: How can you securely generate and distribute the shares over an open network, without compromising your Secret Recovery Phrase?
- SEO Powered Content & PR Distribution. Get Amplified Today.
- PlatoData.Network Vertical Generative Ai. Empower Yourself. Access Here.
- PlatoAiStream. Web3 Intelligence. Knowledge Amplified. Access Here.
- PlatoESG. Automotive / EVs, Carbon, CleanTech, Energy, Environment, Solar, Waste Management. Access Here.
- BlockOffsets. Modernizing Environmental Offset Ownership. Access Here.
- Source: https://www.ledger.com/blog/part-1-genesis-of-ledger-recover-self-custody-without-compromise



