A new Mac-oriented variant of the XLoader infostealer spread widely in the wild last month, signaling a shift in hackers’ ability to effectively target macOS environments.
From mid- to late July, the file “OfficeNote.dmg” was uploaded to VirusTotal nine times, from countries as far and wide as the US, India, Spain, Singapore, and the Philippines. The innocuously named disk image file was actually an updated version of the XLoader infostealer, specially designed to steal credentials from Mac users.
Hackers increasingly have been converting Windows malware for use in macOS environments as of late, but the newest XLoader is far more than just a janky derivative.
“In the past,” says Phil Stokes, a threat researcher at SentinelOne, “it was very common to see cross-platform malware that was a port from a Windows malware, but it was not very effective. The developers didn’t really know how to develop for Mac, right? Well, I think that time is behind us now.”
The New XLoader for Macs
The first XLoader built for Mac environments was discovered two years ago, almost to the day. It was a Java program, which proved to be its Achilles’ heel. The Java Runtime Environment hasn’t been a default element of macOS since Snow Leopard, meaning that XLoader could only work on hosts that had downloaded Java for some reason or another.
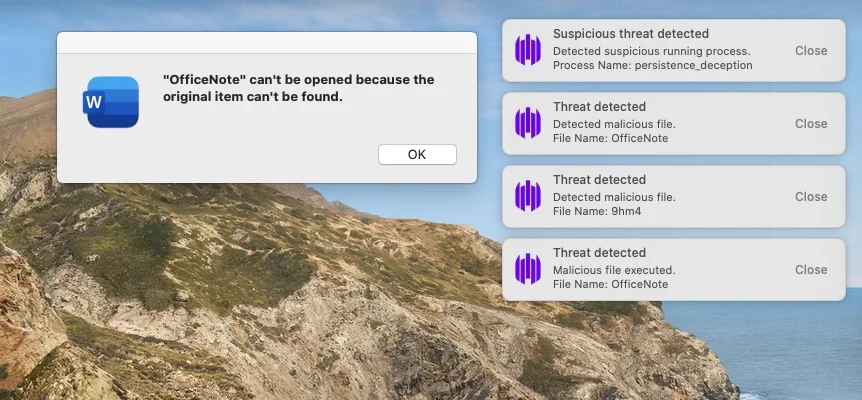
The new XLoader has no such flaw — it’s written natively in C and Objective C. It’s packaged in an application file with the legitimate-sounding name “Office Note,” the macOS Microsoft Word logo, and an Apple developer signature. Apple has since revoked the signature, but “it won’t make much difference,” Stokes says.
“All it means is that the developers will have to pivot to another signature. Developers’ signatures are bought and sold on the Dark Net, or they’re fakes. They can even ad hoc sign, which means it doesn’t actually have a developer signature, but it will still get past Apple’s gatekeeper detection.”
When the file is executed, it will present the user with an error message, while simultaneously installing its payload and a persistence mechanism in the background of the machine.
Once installed, XLoader will attempt to steal credentials saved in Firefox and Chrome, as well as the user’s clipboard.
Notably, at the time of SentinelOne’s publication, Apple’s anti-malware tool XProtect did not have a signature for detecting and blocking OfficeNote.dmg.
The New Face of Mac Malware
Because MacBooks historically have been marketed to individuals rather than industry or big business, they’ve tended to be of less interest to cybercriminals. “Five years ago, there were not very many people who had Macs in the enterprise. Now developers love them, the C-suite loves them, and so they’re great targets. And threat actors will follow wherever the trend is.”
Threat actors began experimenting with Mac malware by unevenly rejiggering existing Windows malware. At best, they would write new malware in languages friendly to both operating systems, like Golang or Rust. “They’re such easy languages for people to learn, and such powerful languages. It’s now much easier to write very good software for different platforms that is going to work out of the box,” Stokes says.
Now, he adds, entire cybercrime teams are dedicated to Mac development. The results are bearing fruit in the form of this new XLoader, but also programs like Atomic Stealer, MacStealer, and PureLand.
The Issue With Apple Security
But to Stokes, it isn’t merely that good malware now exists for MacBooks.
“The problem is that Apple has this kind of attitude to malware, where they take it seriously, but they want it all to be invisible to the user,” he explains. The company’s dogmatic commitment to a seamless, low-effort user experience, which got them so far with consumers in the past, may not be what’s called for in the world of enterprise security.
“If you’ve got a Windows machine, you’ve got a big Microsoft Defender settings page you can go and play with, and run your own scans,” he explains. “Apple’s approach is: We’re going to take care of this silently in the background. And that, for enterprises or businesses of any level, is no good. You cannot have infections going on in the background without your security team knowing about it.”
Time will tell how Apple’s approach to security will stand up to scrutiny. For now, organizations running macOS will need to layer extra security on top of what they’ve got by default.
“The key,” Stokes says, “is businesses should have some other kind of detection, other than just relying on Apple. Just go and make sure you’ve got something that’s giving you that extra visibility and protection.”
- SEO Powered Content & PR Distribution. Get Amplified Today.
- PlatoData.Network Vertical Generative Ai. Empower Yourself. Access Here.
- PlatoAiStream. Web3 Intelligence. Knowledge Amplified. Access Here.
- PlatoESG. Automotive / EVs, Carbon, CleanTech, Energy, Environment, Solar, Waste Management. Access Here.
- PlatoHealth. Biotech and Clinical Trials Intelligence. Access Here.
- ChartPrime. Elevate your Trading Game with ChartPrime. Access Here.
- BlockOffsets. Modernizing Environmental Offset Ownership. Access Here.
- Source: https://www.darkreading.com/vulnerabilities-threats/newer-better-xloader-signals-dangerous-shift-macos-malware



